 Having a device that just prints out paper won’t cut it anymore - today’s printing needs involve much more. Taking care of several needs in a single device is convenient and cost effective, and saves space too.
Having a device that just prints out paper won’t cut it anymore - today’s printing needs involve much more. Taking care of several needs in a single device is convenient and cost effective, and saves space too.
These days, printers have become more than just, well, printers. There are many additional features and factors to consider for your purchase, as well as its use, to be as cost effective as possible.
Multi-functionality is one of the most important factors you should consider when buying a printer. With technology moving in leaps and bounds, having a device that just prints out paper won’t cut it anymore. Today’s printers have multiple functions, which make them more versatile. Look for features such as a built in scanner (preferably capable of multiple page scanning), as well as fax and copy options. It’s much more convenient to have everything in a single device, and it saves space too.
Another factor to consider is how economical your printer will be to use. One feature that helps reduce costs is called duplex printing, which allows you to print on both sides of the page - saving on paper costs and making your operations much more environment friendly. Make sure that your printer has the option of setting duplex printing as its default mode.
Another way to save is by determining which type of printer you need - laser or inkjet. Inkjet printers print slower, but are cheaper to purchase and use. Laser printers print faster and offer better quality output, but are much more expensive to purchase, and the ink cartridges cost a lot more, too. So before buying a printer, it’s essential to determine how you’ll use it first.
Also make sure that your printer has the option to print draft and black-only copies for not-so-important documents. When you don’t need professional quality or color prints you should have the option to enable lower quality printing, which will save on ink costs.
You should also look into network printing, which lets multiple users print from a single printer. This enables you to monitor ink and paper usage better, and also eliminates the need for multiple printers in the office, saving on purchase, operation, and maintenance costs. An LCD on your printer will also help you diagnose and troubleshoot problems, as well as preview documents that are printing or in the cue.
If you are looking for help in buying a new printer for your office, or want to organize your existing printing system to save on costs, please feel free to give us a call so we can discuss options that will meet your particular needs.

 Patching and updating the programs that you use, as well as removing old or unused programs, can go a long way in ensuring that your system is safe from malware attacks.
Patching and updating the programs that you use, as well as removing old or unused programs, can go a long way in ensuring that your system is safe from malware attacks. A Business Community Plan allows your business to resume normal operations after experiencing data loss or equipment failure resulting from minor problems to major disasters.
A Business Community Plan allows your business to resume normal operations after experiencing data loss or equipment failure resulting from minor problems to major disasters. Twitter can be a powerful tool for business if used properly, but how? Experts list a few tips to help you utilize this social networking website to boost your online presence.
Twitter can be a powerful tool for business if used properly, but how? Experts list a few tips to help you utilize this social networking website to boost your online presence. Passwords are more or less the equivalent of keys when it comes to cyberspace. However, passwords can be compromised through hacking, stealing, or even just guessing – which is why password security and integrity is very important.
Passwords are more or less the equivalent of keys when it comes to cyberspace. However, passwords can be compromised through hacking, stealing, or even just guessing – which is why password security and integrity is very important. You can avoid computer problems with Managed IT Services. IT professionals will conduct a comprehensive analysis of your IT processes and functions and help you assess how to produce the most favorable results for your business.
You can avoid computer problems with Managed IT Services. IT professionals will conduct a comprehensive analysis of your IT processes and functions and help you assess how to produce the most favorable results for your business. As businesses and business people store more and more important information in their smartphones, the smart thing to do is to have a plan in place in case you lose it - having your smartphone’s data in the wrong hands can be a potential nightmare.
As businesses and business people store more and more important information in their smartphones, the smart thing to do is to have a plan in place in case you lose it - having your smartphone’s data in the wrong hands can be a potential nightmare. Without us knowing, we may visit websites that aren’t exactly healthy for our systems - inviting malware, phishing, and all types of potentially unsavory viruses that can damage our systems. The solution is simple: Clear Cloud
Without us knowing, we may visit websites that aren’t exactly healthy for our systems - inviting malware, phishing, and all types of potentially unsavory viruses that can damage our systems. The solution is simple: Clear Cloud Microsoft recommends transferring to Windows 7 as Microsoft XP ceased sales on October 22, 2010, with support available only until April 2014.
Microsoft recommends transferring to Windows 7 as Microsoft XP ceased sales on October 22, 2010, with support available only until April 2014.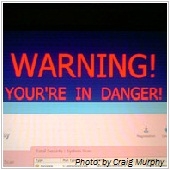 Since MS Word and Adobe Reader are widely used applications, hackers and malware designers have come up with ways to exploit these programs and the documents associated with them in order to infect as many people possible.
Since MS Word and Adobe Reader are widely used applications, hackers and malware designers have come up with ways to exploit these programs and the documents associated with them in order to infect as many people possible.
